In the intricate world of digital security, where trust and authentication are paramount, Public Key Infrastructure (PKI) serves as the backbone, enabling secure communications and verifying identities. At the heart of a robust PKI deployment lies the Certificate Authority (CA), the trusted entity responsible for issuing and managing digital certificates. For organizations seeking to streamline their certificate issuance processes, enforce consistent security policies, and reduce administrative overhead, understanding and effectively utilizing Certificate Authority Templates becomes indispensable. These templates act as pre-defined blueprints, dictating the properties and requirements for various types of certificates, ensuring uniformity and adherence to organizational standards.
The strategic application of these templates transforms a potentially chaotic manual process into an efficient, automated system. Without them, administrators would face the arduous task of manually configuring each certificate, leading to inconsistencies, human error, and a significant drain on resources. This is particularly true in large enterprises with diverse cryptographic needs, ranging from user authentication and email encryption to secure web server communication and code signing.
By leveraging well-designed templates, an organization can codify its security policies directly into the certificate issuance process. This ensures that every certificate issued for a specific purpose meets the necessary cryptographic standards, validity periods, key usage restrictions, and other critical attributes. The adoption of such a systematic approach not only enhances security but also significantly improves operational efficiency, making it a cornerstone of modern PKI management.
This comprehensive guide will delve into the intricacies of Certificate Authority templates, exploring their components, best practices for their design and implementation, and their vital role in maintaining a secure and manageable digital environment. From understanding their core functionality to advanced management techniques, we will cover the essential knowledge required to harness the full power of these critical PKI elements.

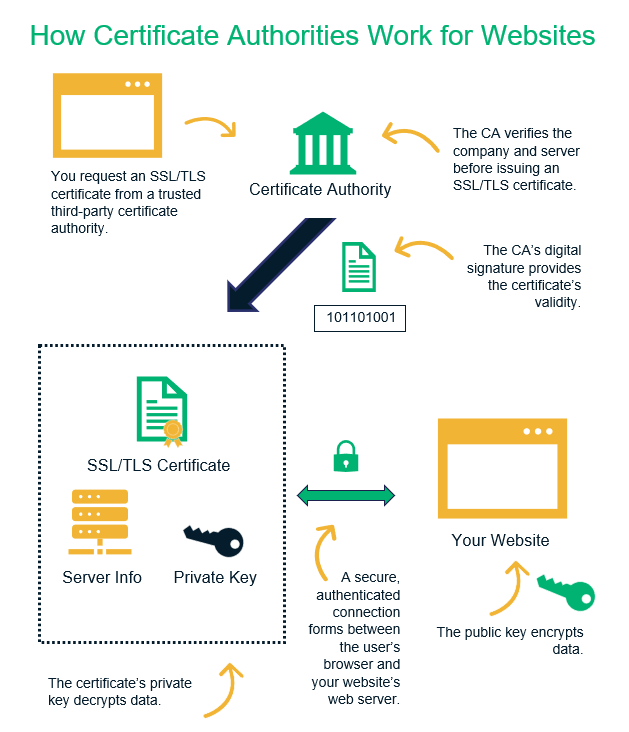
A Certificate Authority (CA) is a trusted third party that issues digital certificates. These certificates serve as digital passports, verifying the identity of individuals, devices, or services in a network. CAs are foundational to Public Key Infrastructure (PKI), which provides the framework for encrypting and signing data, as well as authenticating users and systems. When you connect to a secure website, send an encrypted email, or log into a corporate network, a digital certificate issued by a CA is often involved, providing the assurance that the entity you’re interacting with is legitimate.

The CA’s primary role is to bind a public key to an identified entity, such as a person or a server, and to cryptographically sign this binding in the form of a certificate. This signature acts as a guarantee that the CA has verified the identity of the certificate holder. The trust model typically involves a hierarchy, with a root CA at the top, whose certificate is self-signed and distributed widely as a trusted anchor, and one or more issuing (or subordinate) CAs that issue certificates to end-entities. This structure ensures scalability and allows for the delegation of certificate issuance responsibilities.

Certificate Authority Templates are pre-configured sets of rules and settings that define the characteristics of a digital certificate. Instead of manually specifying every attribute for each certificate request, administrators can select an appropriate template, streamlining the issuance process significantly. This automation is not merely about convenience; it is a critical component for maintaining security, consistency, and compliance across an organization’s digital assets.
Templates dictate crucial parameters such as the certificate’s intended purpose (e.g., server authentication, client authentication, code signing), cryptographic algorithms allowed (e.g., RSA, ECDSA), key lengths, validity periods, and whether the certificate can be renewed automatically. By standardizing these attributes, organizations can prevent misconfigurations, enforce adherence to security policies, and ensure that all certificates issued within a specific category meet the required security profile. For instance, a template for web servers might mandate a minimum 2048-bit RSA key and a 365-day validity period, while a client authentication template might allow for shorter validity and different key usages.

The advantages of implementing well-designed Certificate Authority Templates are numerous:

Designing effective Certificate Authority Templates requires a thorough understanding of their various configurable components. Each element plays a vital role in defining the behavior and attributes of the certificates issued based on that template.
This section defines how the identity of the certificate holder will be represented. It can specify whether the subject name should be built from Active Directory (AD) information, supplied by the requester, or constructed from other sources. Options typically include Common Name (CN), Organizational Unit (OU), Organization (O), Locality (L), State (S), and Country (C). For machine certificates, the DNS name is often critical.

Extensions add specific information to the certificate, detailing its capabilities and restrictions. Key extensions include:
This component dictates the cryptographic properties of the certificate:
These settings control who can request a certificate from the template and how many approvers are needed:
This simply defines the duration for which the issued certificate will be considered valid. Common periods are 1 year, 2 years, or 5 years. A shorter validity period enhances security by limiting the window of exposure if a private key is compromised but increases administrative overhead for renewals.
Different scenarios demand different certificate characteristics, leading to the creation of various Certificate Authority Templates, each tailored for specific purposes.
These templates are designed for servers hosting websites and web services. They typically include Server Authentication in their Extended Key Usage (EKU) and often mandate a Subject Alternative Name (SAN) extension for multiple domain names. Strong cryptographic settings (e.g., RSA 2048-bit or higher, SHA256) and a 1-2 year validity period are common.
Used for authenticating individual users or devices to network resources, VPNs, Wi-Fi networks, or applications. Their EKU will include Client Authentication. These templates might allow for auto-enrollment and typically integrate with user accounts in Active Directory, pulling subject information directly.
These templates are used for signing and encrypting email communications, providing non-repudiation and confidentiality. The EKU would include Secure Email and potentially Digital Signature and Key Encipherment. They are usually tied to user accounts and might allow for private key export if users need to install the certificate on multiple devices.
Essential for developers to digitally sign software, scripts, and applications, assuring users of the software’s authenticity and integrity. The EKU will specify Code Signing. These templates often have stricter key protection requirements and might be managed by a separate group within the organization.
Similar to client authentication but specifically for machines (e.g., workstations, servers) to authenticate to network services or other devices. The EKU usually includes Client Authentication or Device Authentication. These are often set up for auto-enrollment for all machines within a specific domain or organizational unit.
Critical for Active Directory security, these certificates authenticate domain controllers to each other and to clients, enabling secure LDAP and Kerberos authentication. They typically include KDC Authentication, Server Authentication, and Client Authentication EKUs.
The success of your PKI deployment heavily relies on the thoughtful design and meticulous implementation of your Certificate Authority Templates. This isn’t a “set it and forget it” task but rather a strategic planning exercise.
Before creating any template, define your organizational security policies. What are the minimum key lengths required? What are the allowed validity periods for different certificate types? Who needs to approve certificate requests? How will certificates be revoked or renewed? Document these policies, as they will directly translate into your template settings. Consider compliance requirements (e.g., industry standards, government regulations) that might dictate specific cryptographic algorithms or certificate attributes.
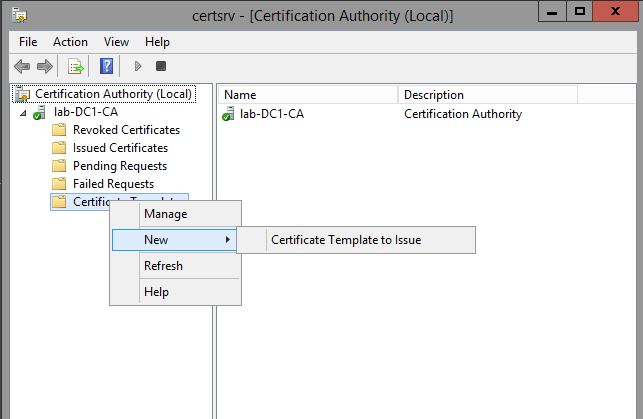
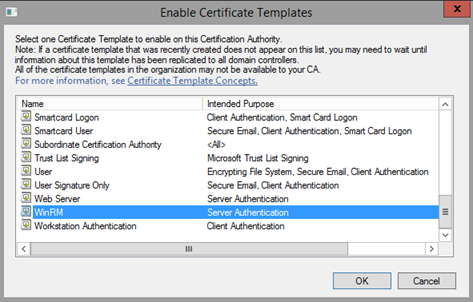
Once templates are designed, they need to be published to the Certificate Authority. Thorough testing is crucial. Issue test certificates using each new or modified template and verify that:
The lifecycle of Certificate Authority Templates extends beyond initial creation. Effective management is essential to adapt to evolving security threats, technological advancements, and organizational needs.
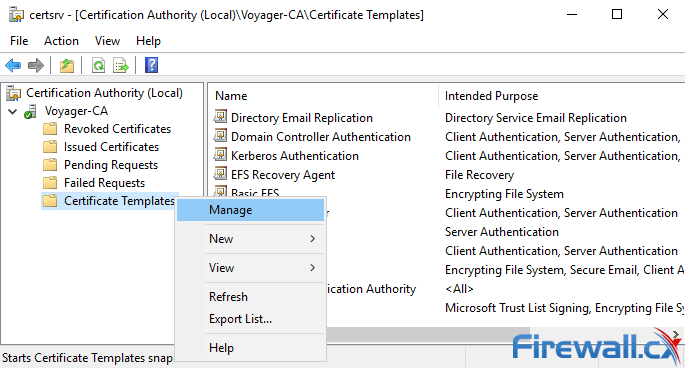
When a security vulnerability is discovered in a cryptographic algorithm, or an organization decides to move to stronger key lengths, existing templates may need to be updated. Instead of directly modifying a live template, it’s often best practice to create a new version of the template. This allows administrators to:
Existing certificates issued from the old template will remain valid until their expiration or revocation, while new requests can be directed to the updated template.
Regularly review issued certificates to ensure they align with the intended template configurations. Audit CA logs for failed certificate requests, unauthorized template access attempts, or any unusual activity. This continuous monitoring helps in identifying misconfigurations or potential security breaches early on.
When a template is no longer needed (e.g., an application is deprecated, or a security policy changes significantly), it should be retired. This involves unpublishing the template from the CA to prevent further issuance. Consider archiving the template configuration for historical records or future reference.
Even with careful planning, issues can arise with Certificate Authority Templates. Understanding common problems and advanced configurations can significantly aid in PKI management.
For Windows-based CAs, integration with Active Directory is a powerful feature that simplifies certificate management. Templates can leverage AD attributes to populate certificate subject fields, define user and computer auto-enrollment, and apply security permissions based on AD groups. This tight integration is a cornerstone of efficient enterprise PKI.
Use RBAC to manage permissions on templates. Instead of assigning individual users, create security groups in Active Directory (e.g., “PKI Admins,” “Web Server Admins”) and assign permissions to these groups. This simplifies management and enhances security.
Protecting your Certificate Authority Templates is paramount. Ensure that only authorized personnel have “Write” permissions on templates, as this allows modification of critical settings. Restrict who can publish or unpublish templates from the CA. Implement strong authentication for CA administrators and regularly audit access logs.
Certificate Authority Templates are more than just a convenience; they are a fundamental pillar of a secure, efficient, and scalable Public Key Infrastructure. By providing a structured framework for certificate issuance, they enforce consistency, reduce manual errors, and align cryptographic assets with organizational security policies. From defining cryptographic standards and validity periods to dictating key usages and subject information, these templates ensure that every certificate issued serves its intended purpose securely.
Effective design, meticulous implementation, and ongoing management of these templates are critical for any organization relying on digital certificates for authentication, encryption, and digital signatures. As the digital landscape continues to evolve, understanding and leveraging the full potential of Certificate Authority Templates will remain an essential skill for IT professionals dedicated to maintaining robust and resilient cybersecurity defenses. Investing in their careful configuration is an investment in the long-term integrity and trustworthiness of your entire digital ecosystem.