Security assessments are a critical part of any organization’s risk management strategy. Regularly scanning systems for vulnerabilities and understanding the potential impact of those vulnerabilities is essential for maintaining a strong security posture. One of the most valuable tools in this process is Nessus, a widely-used vulnerability scanner. But navigating the vast amount of data generated by Nessus can be daunting. That’s where Nessus Report Templates come in – they offer a streamlined way to organize and present your findings, making it easier to understand, share, and act upon the information. This article will delve into the world of Nessus Report Templates, exploring their benefits, different types, and how to effectively utilize them to improve your security analysis workflow.
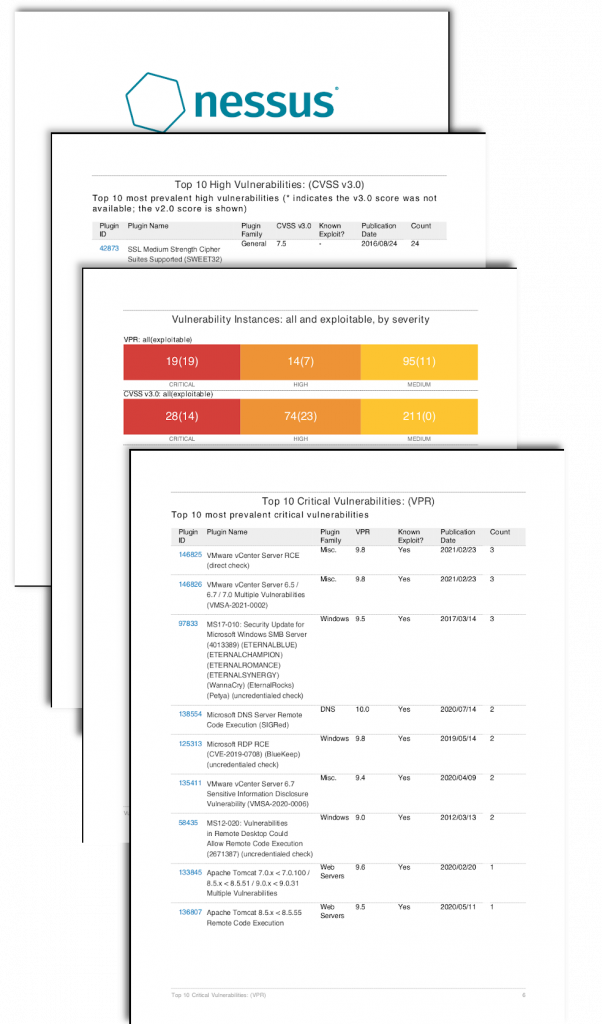
Nessus Report Templates are pre-formatted documents that automatically generate reports based on your scans. They’re not just a simple summary; they’re a structured approach to presenting your findings, saving you time and effort. The core concept is that Nessus automatically identifies vulnerabilities, categorizes them, and presents them in a clear, consistent format. This is particularly beneficial for teams that need to collaborate on security assessments, or for individuals who need to quickly understand the scope of a scan. The ability to customize these templates allows for tailored reporting, ensuring that the information is relevant to your specific needs. Without these templates, manually compiling reports from numerous scans would be a laborious and error-prone process. They represent a significant improvement in efficiency and accuracy.
The advantages of adopting Nessus Report Templates are numerous and contribute to a more robust security program. Firstly, they drastically reduce the time spent on report creation. Instead of manually constructing reports from individual scan results, you can leverage a pre-built template. Secondly, they ensure consistency across all scans. Each report will adhere to a standardized format, making it easier to compare findings and identify patterns. Thirdly, they facilitate collaboration. Multiple team members can work on the same template, ensuring everyone is aligned on the key findings and recommendations. Finally, they improve auditability. The structured format makes it easier to track changes and demonstrate compliance with security standards. Ultimately, investing in Nessus Report Templates is an investment in a more efficient and effective security program.
Nessus offers a variety of report templates catering to different needs and levels of detail. The most common types include:
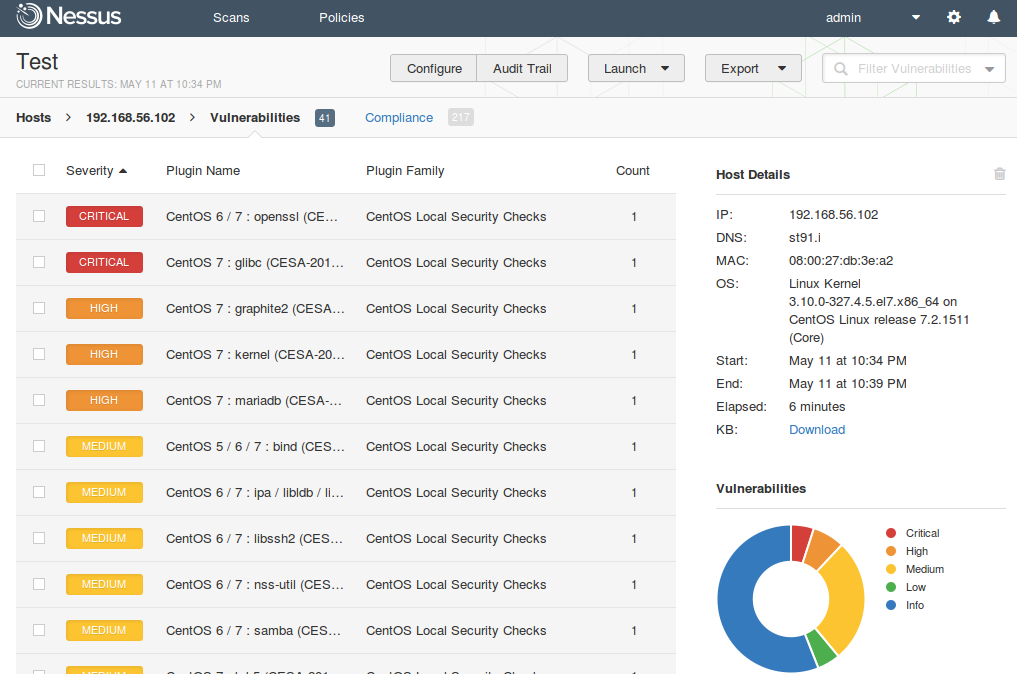
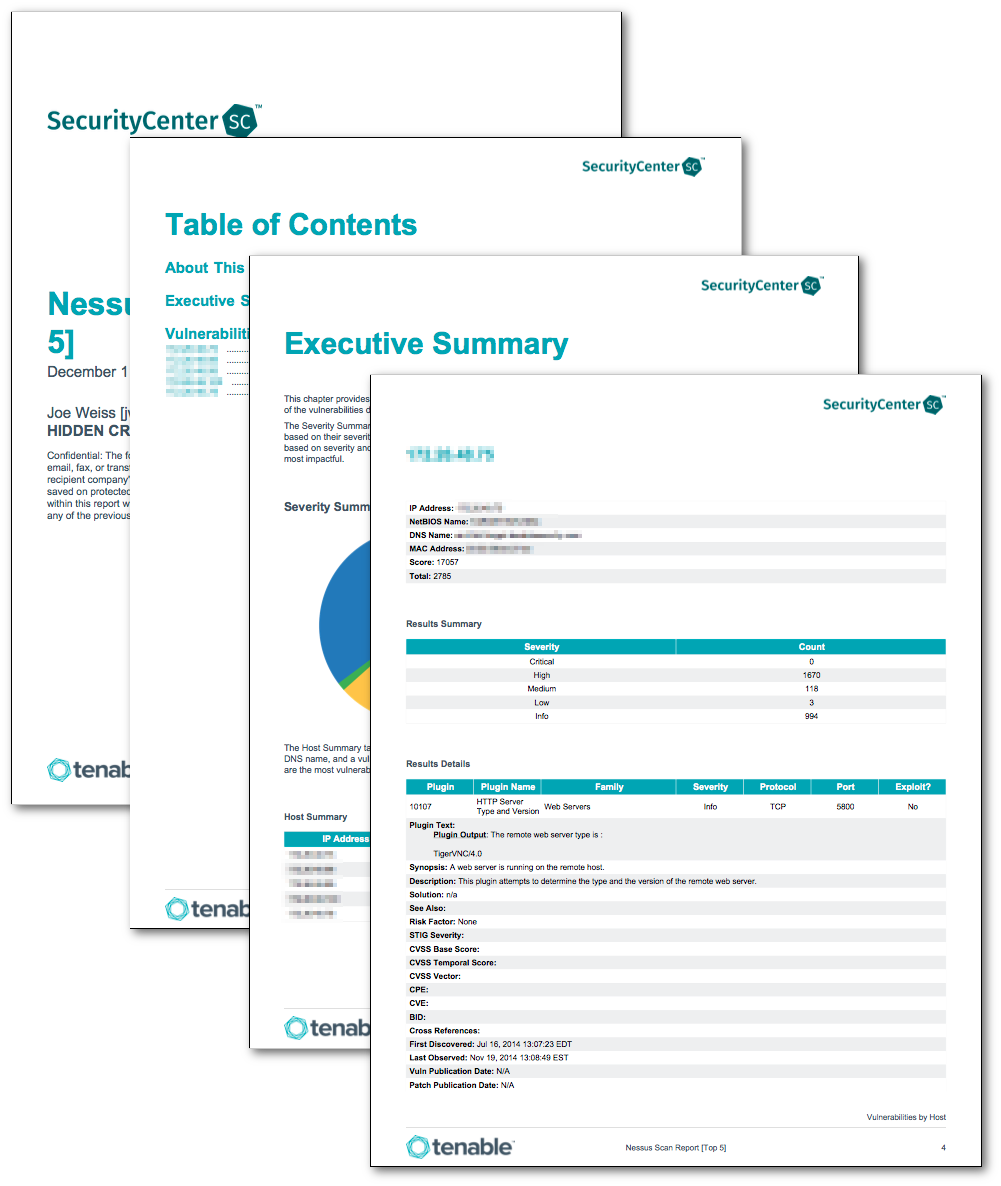
This is the foundational template, providing a comprehensive overview of your scans. It typically includes a summary of vulnerabilities, their severity levels, and recommended remediation steps. It’s a good starting point for initial assessments and provides a broad understanding of the security landscape. The standard report is often a good choice for larger organizations needing a high-level overview.
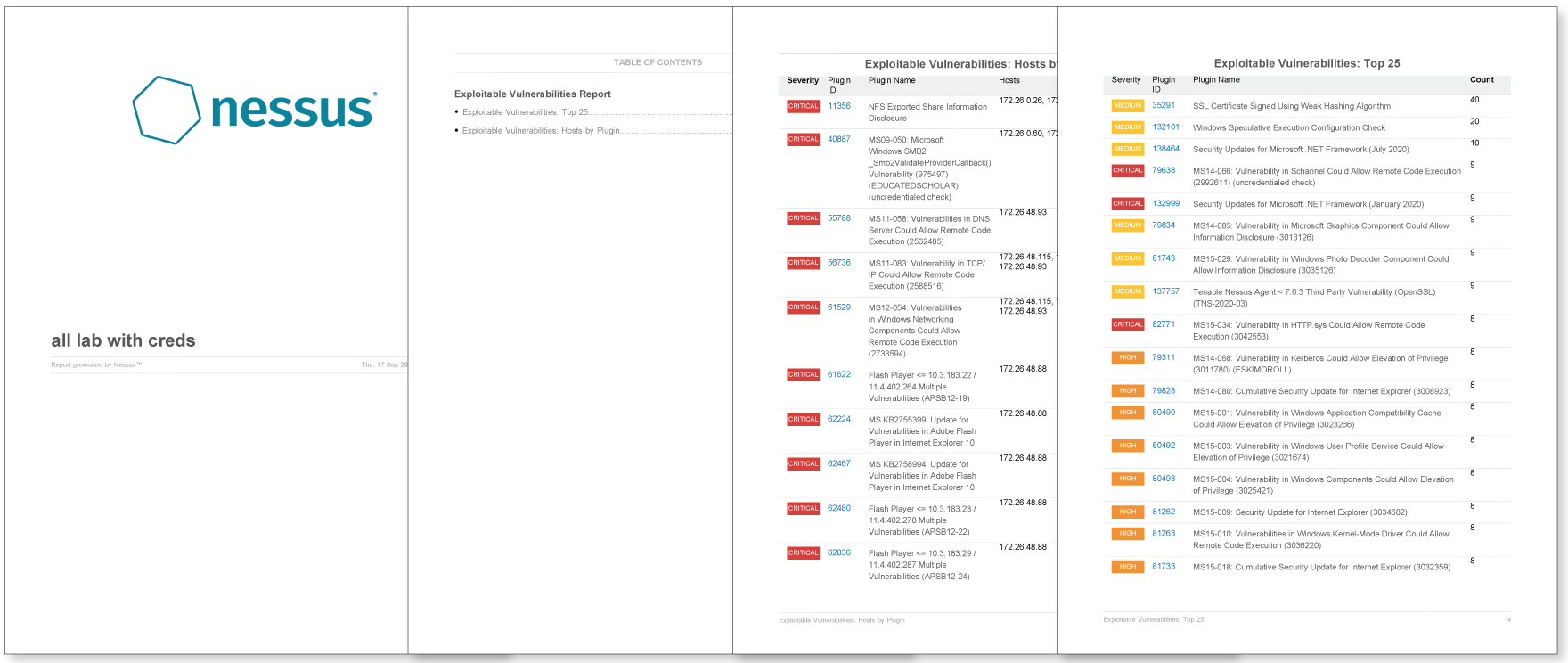
This template goes deeper into the specifics of each vulnerability. It provides detailed information about the vulnerability, including its description, affected systems, potential impact, and remediation recommendations. It’s ideal for situations where a thorough understanding of the vulnerability’s implications is crucial. This template is frequently used by security analysts for detailed investigation.
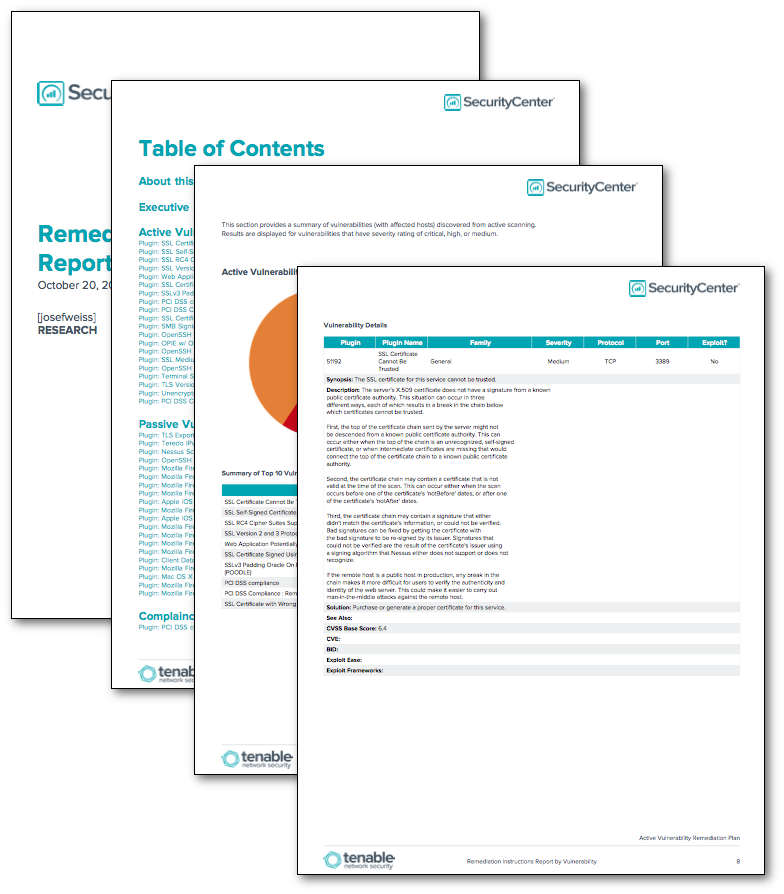
This template focuses specifically on the remediation steps required to address the identified vulnerabilities. It outlines the recommended actions, such as patching, configuration changes, or other security controls. It’s invaluable for prioritizing remediation efforts and ensuring that vulnerabilities are addressed promptly. This is often the most utilized template for driving action.
Tailored for regulatory compliance (e.g., PCI DSS, HIPAA), this template emphasizes the findings related to specific compliance requirements. It includes specific data handling, access control, and security controls that must be met. This is particularly important for organizations operating in regulated industries.
For organizations with unique security requirements, custom report templates can be created. These templates allow you to tailor the report to include specific data, metrics, and visualizations relevant to your organization’s needs. This level of customization provides maximum flexibility.

The true power of Nessus Report Templates lies in their effective utilization. Here are some best practices:
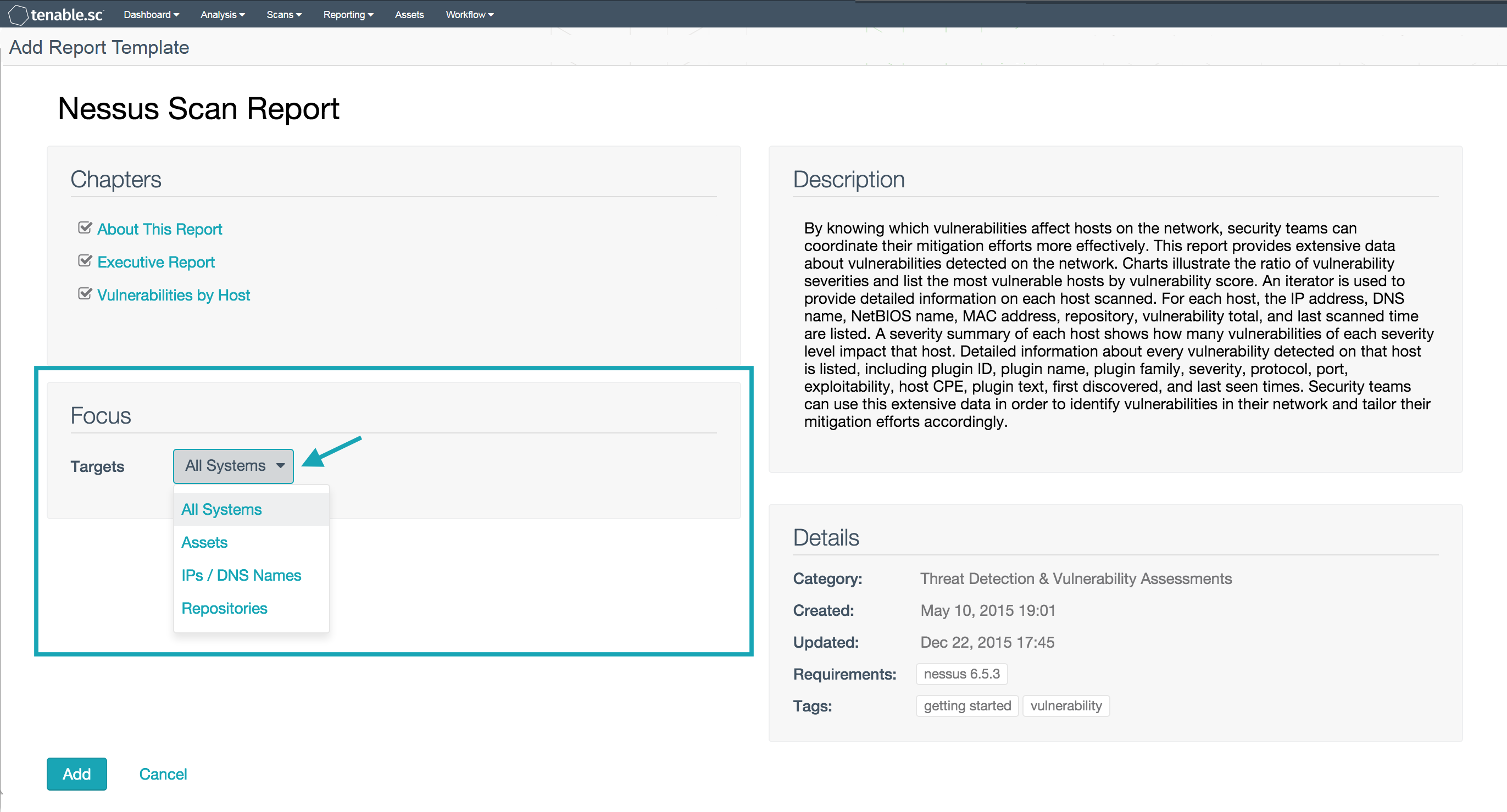
Don’t just accept the default settings. Customize the template to include relevant data and metrics. Add your own notes, annotations, and recommendations to provide context and guidance.
Nessus automatically captures metadata about each scan, such as the date, time, and system affected. Utilize this metadata to filter and analyze your reports.
Whenever possible, process scans in batches to improve efficiency. This allows you to quickly generate reports for multiple systems.
Consider automating the report generation process using scripting or other automation tools. This can significantly reduce manual effort and improve consistency.
Always review and validate the generated reports before sharing them with stakeholders. Ensure that the information is accurate and complete.
Nessus Report Templates are an indispensable tool for any organization seeking to improve its security posture. By streamlining the reporting process, ensuring consistency, facilitating collaboration, and improving auditability, they significantly enhance the effectiveness of security assessments. Investing in these templates is a strategic move that will pay dividends in terms of reduced risk, improved efficiency, and a more proactive security program. As Nessus continues to evolve, the availability and sophistication of these templates will undoubtedly continue to grow, further solidifying their position as a cornerstone of modern security analysis. Ultimately, mastering the use of Nessus Report Templates empowers security teams to make informed decisions and proactively defend against evolving threats.