The world of cybersecurity is constantly evolving, presenting organizations with a never-ending stream of potential threats. Effectively managing these risks requires a structured approach – a robust Threat Assessment Report Template is an invaluable tool. This template provides a framework for systematically identifying, analyzing, and prioritizing threats, enabling organizations to proactively defend against potential attacks. A well-crafted Threat Assessment Report Template isn’t just a document; it’s a strategic asset, fostering informed decision-making and ultimately, enhanced security posture. It’s a foundational element of any comprehensive cybersecurity strategy. This article will delve into the key components of a successful Threat Assessment Report Template, offering practical guidance and best practices for its creation and utilization. Understanding the importance of this template is crucial for any organization seeking to safeguard its assets and maintain operational resilience. Let’s explore how to build a powerful tool for proactive threat management.
Before diving into the specifics of the template, it’s important to grasp the underlying principles that drive its effectiveness. A successful Threat Assessment Report Template isn’t simply a checklist; it’s a process. It begins with a clear understanding of the organization’s risk profile and its specific vulnerabilities. This involves a thorough assessment of existing security controls, data flows, and potential attack vectors. The process should be iterative, continually refined as new threats emerge and vulnerabilities are discovered. Furthermore, the template must be adaptable – it should accommodate the unique characteristics of each organization and its industry. Ignoring these foundational elements will result in a flawed assessment, rendering it ineffective. Ultimately, the goal is to move beyond reactive security measures and embrace a proactive, risk-based approach.
The first step in constructing a comprehensive Threat Assessment Report Template is clearly defining the scope and objectives. What specific assets are being assessed? What types of threats are of primary concern? Are there specific regulatory requirements or industry standards that must be considered? For example, a financial institution’s Threat Assessment Report Template would prioritize threats related to financial data theft and ransomware attacks, while a healthcare provider’s template might focus on HIPAA compliance and patient data breaches. Clearly articulating these objectives will guide the assessment process and ensure that the report delivers the most relevant information. It’s vital to establish a baseline understanding of the organization’s current security posture – what’s already in place, and where are the gaps? This baseline will serve as a benchmark against which to measure progress and identify areas for improvement. Without a well-defined scope, the assessment risks becoming unfocused and unproductive.
Once the scope and objectives are established, the next crucial step is gathering threat intelligence. This involves identifying potential threats and vulnerabilities through a variety of sources. These sources can include:
The quality and timeliness of threat intelligence are critical to the success of the assessment. A fragmented or outdated threat intelligence environment can significantly compromise the accuracy and usefulness of the report. It’s important to establish a process for regularly updating threat intelligence feeds and verifying the accuracy of collected information.
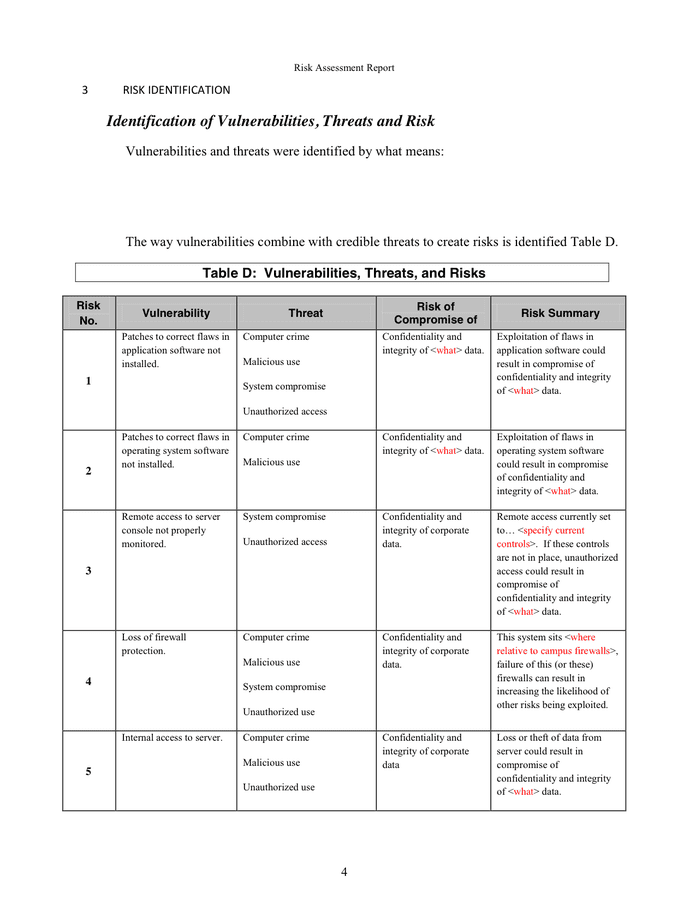
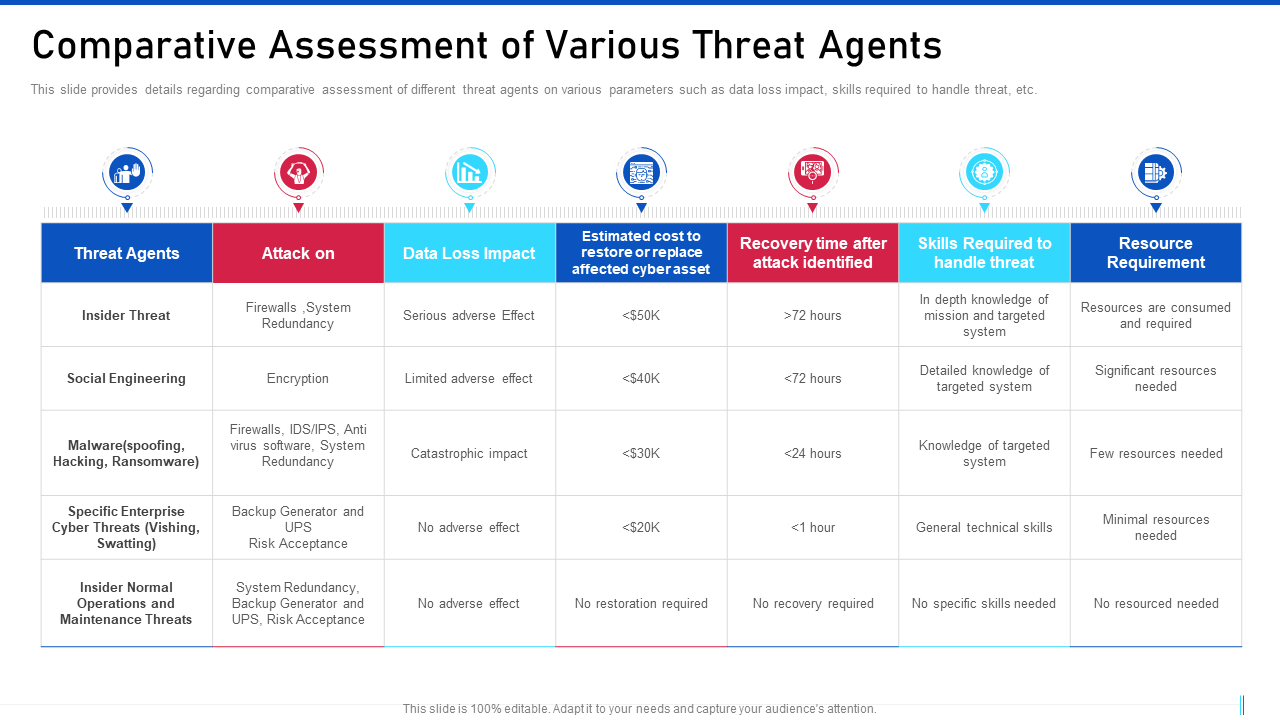
With threat intelligence gathered, it’s time to analyze the data and identify potential threats. This involves a systematic process of identifying patterns, trends, and indicators of compromise. Several techniques can be employed:
The analysis phase should consider both known and potential threats, taking into account the organization’s specific environment and risk tolerance. It’s important to remember that threats can be complex and multifaceted, requiring a holistic approach to analysis.

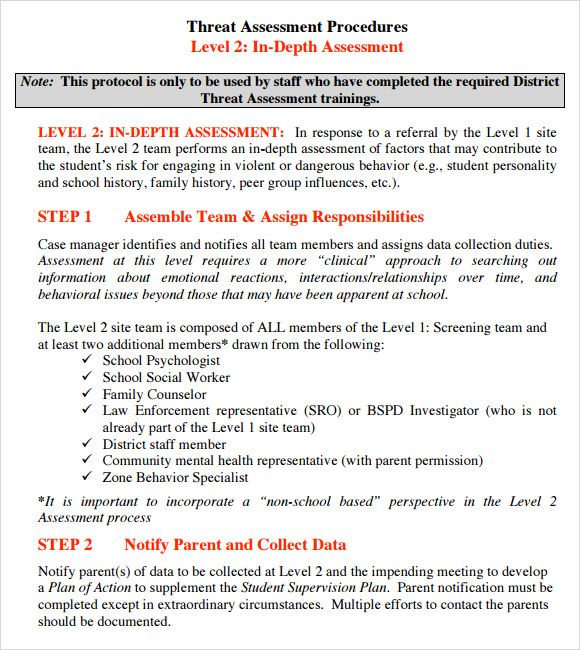
Once threats are identified, it’s time to assess the vulnerabilities that could be exploited. This involves evaluating the technical controls and configurations that could be bypassed. Common assessment methods include:
The assessment should focus on identifying vulnerabilities that could be exploited by attackers. It’s important to prioritize vulnerabilities based on their potential impact and likelihood of exploitation. A thorough assessment should include a detailed description of each vulnerability, its potential impact, and recommended remediation steps.
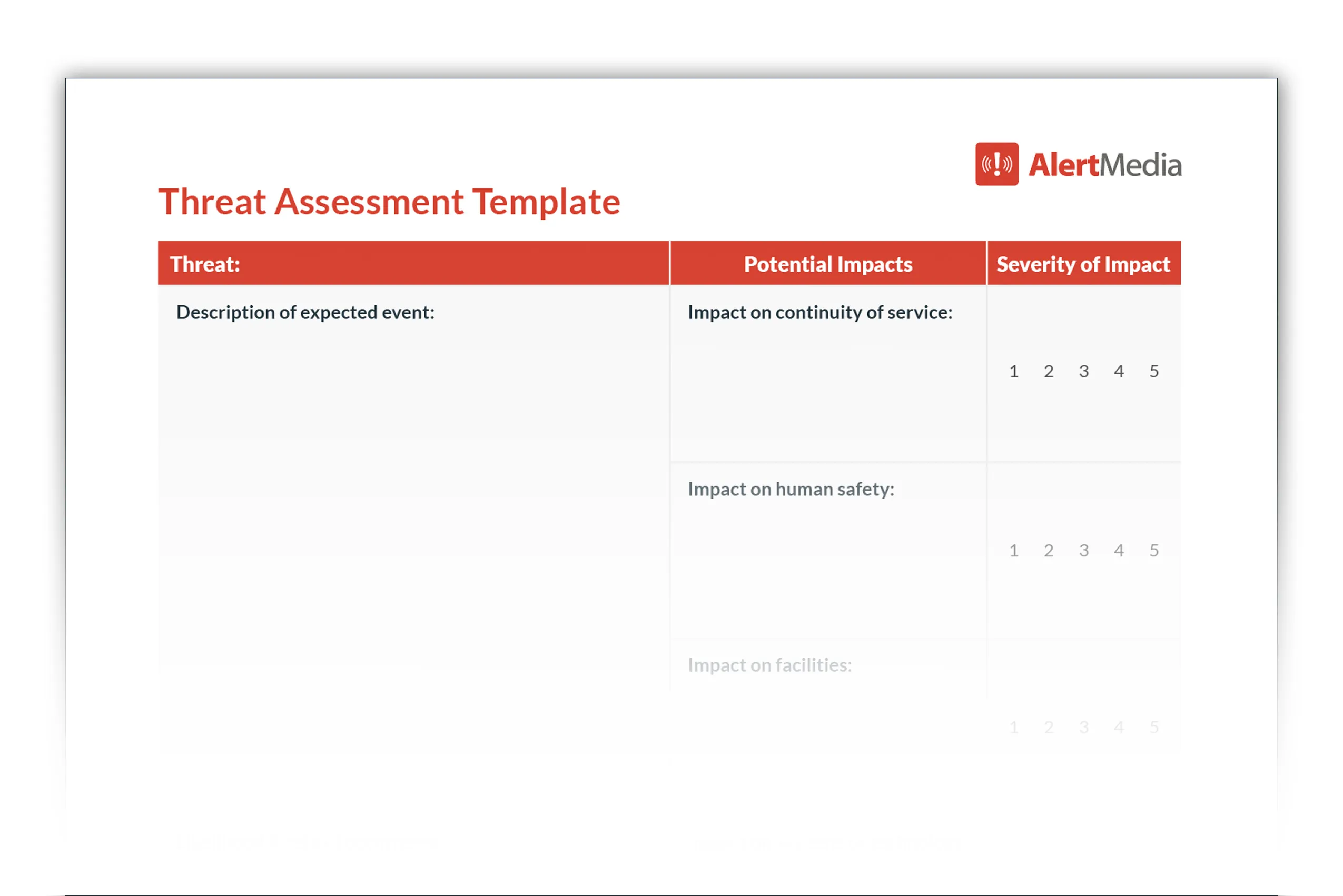
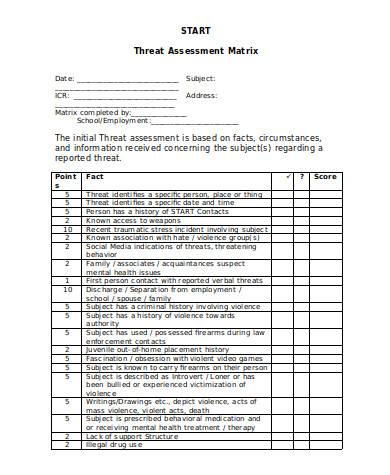
After assessing vulnerabilities, it’s crucial to prioritize risks based on their potential impact and likelihood of exploitation. A risk scoring system is commonly used to facilitate this process. This typically involves assigning a risk score to each identified threat, based on factors such as:
The risk score is then used to prioritize remediation efforts. High-risk vulnerabilities should be addressed first. The Threat Assessment Report Template should include a clear plan for managing identified risks, including timelines, responsibilities, and resource allocation.
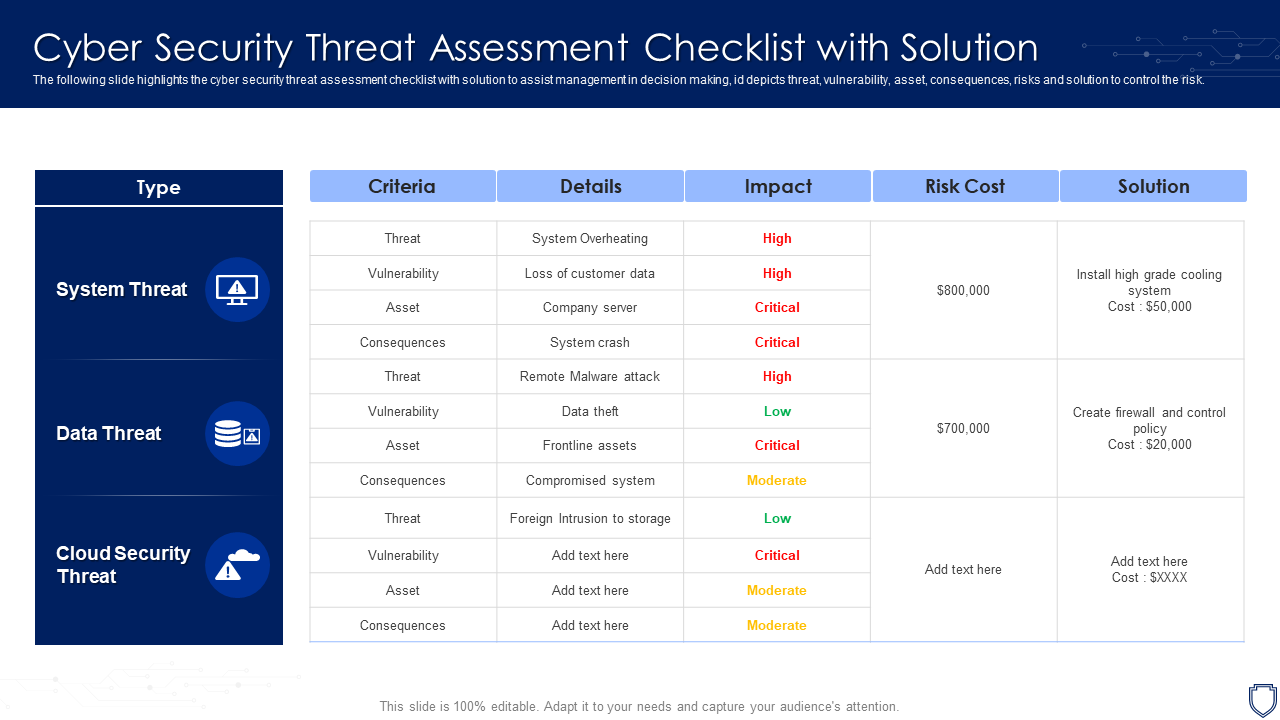
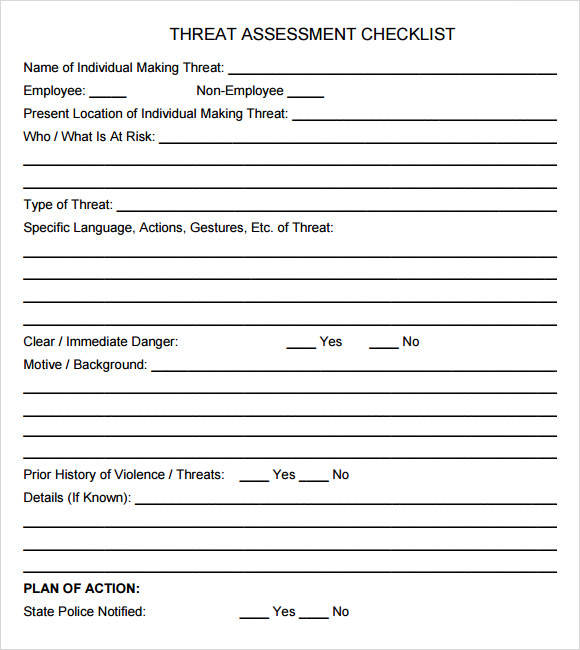
The final section of the Threat Assessment Report Template is dedicated to reporting the findings and providing recommendations. This section should clearly communicate the assessment results to stakeholders, including management, IT staff, and security teams. The report should include:
The report should be presented in a clear and concise manner, using visuals and diagrams to enhance understanding. It should be tailored to the needs of the audience, providing the information they need to make informed decisions.
The Threat Assessment Report Template is a critical component of any organization’s cybersecurity strategy. By systematically identifying, analyzing, and prioritizing threats, this template enables organizations to proactively defend against potential attacks and maintain operational resilience. A well-executed Threat Assessment Report Template fosters a culture of security awareness, promotes informed decision-making, and ultimately, contributes to a more secure environment. Investing in the creation and maintenance of a robust Threat Assessment Report Template is an investment in the long-term security of the organization. Continuous improvement and adaptation are key to staying ahead of evolving threats. As the threat landscape continues to change, the Threat Assessment Report Template must evolve alongside it, ensuring that the organization remains prepared for the challenges ahead.